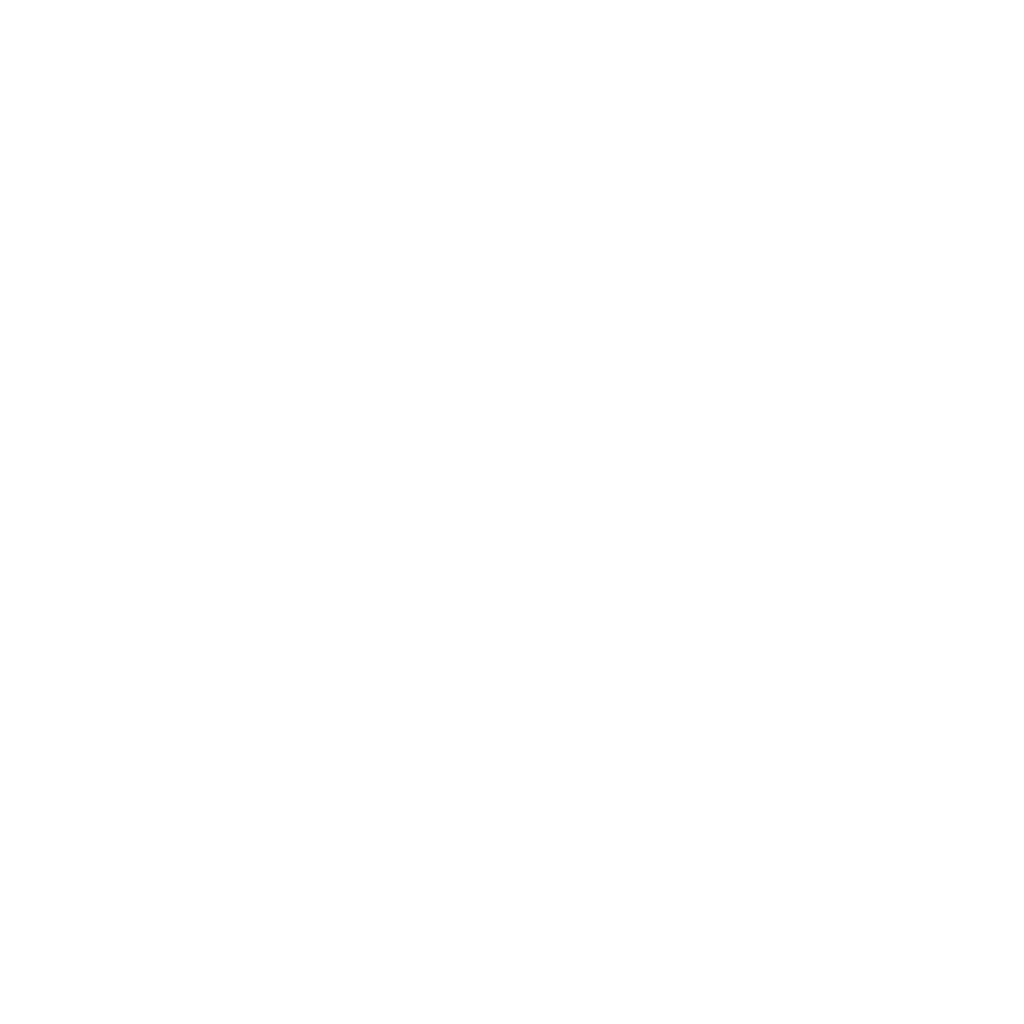
We discuss Active Defense, moving beyond a passive approach to detection. How can we intentionally shape threat actor behavior via Controlled Attack Paths and Cyber Deception? Defenders inadvertently influence attackers by the way they configure layered defenses, impacting attack preferences.
intercepting fist
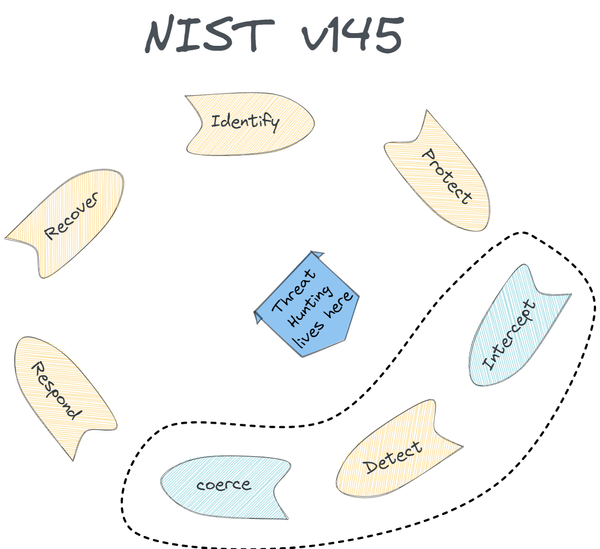
While Threat Hunting is commonly seen as proactive threat detection, we propose a broader approach through the lens of Active Defense. This involves intercepting and disrupting adversaries with the goal of actively shaping attacker behavior rather than relying solely on detection.